
LinkedIn “Social Engineering”: Protecting Your Staff from Fake Recruitment Scams
A fake recruiter message is one of the cleanest social engineering tricks around because it doesn’t look like a trick. That’s why LinkedIn recruitment scams


A fake recruiter message is one of the cleanest social engineering tricks around because it doesn’t look like a trick. That’s why LinkedIn recruitment scams

In the traditional office, a “Clean Desk” policy was a simple habit: shred the sensitive stuff, lock it away, and don’t leave passwords where someone

At home, security incidents don’t look like dramatic movie hacks. They look like stepping away from your laptop during a delivery, or leaving it unlocked

If you want to uncover unsanctioned cloud apps, don’t begin with a policy. Start with your browser history. The cloud environment most businesses actually use
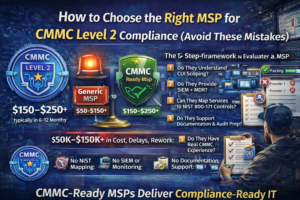
How to Choose the Right MSP for CMMC Level 2 Compliance (Avoid These Mistakes) Choosing the wrong MSP for CMMC Level 2 compliance can cost
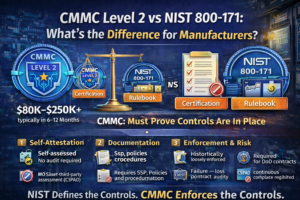
CMMC Level 2 vs NIST 800-171: What’s the Difference for Manufacturers? CMMC Level 2 and NIST 800-171 are closely related—but not the same. NIST 800-171

Why Phishing Attacks Are Increasing in 2026 (and How Microsoft 365 Direct Send Spoof Protection Helps) Phishing attacks have increased by an estimated 50–70% over

Ransomware isn’t a jump scare. It’s a slow build. In many cases, it begins days, or even weeks, before encryption, with something mundane, like a

What Happens If You Fail a CMMC Level 2 Assessment? Failing a CMMC Level 2 assessment can result in lost DoD contracts, delayed revenue, and

Do You Need a 24/7 SOC for CMMC Level 2 Compliance? For most aerospace and DoD supply chain manufacturers, a 24/7 Security Operations Center (SOC)

It usually starts small. Someone uses an AI tool to refine a difficult email. Someone enables an AI add-on inside a SaaS app because it
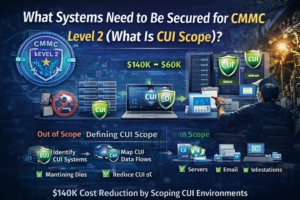
For manufacturers pursuing CMMC Level 2 compliance, only systems that store, process, or transmit Controlled Unclassified Information (CUI) need to be secured—but defining that scope
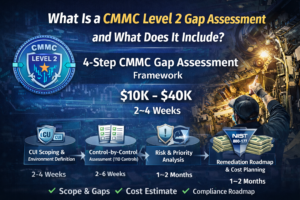
What Is a CMMC Level 2 Gap Assessment and What Does It Include? A CMMC Level 2 gap assessment typically costs between $10,000 and $40,000

Most small businesses aren’t breached because they have no security at all. They’re breached because a single stolen password becomes a master key to everything
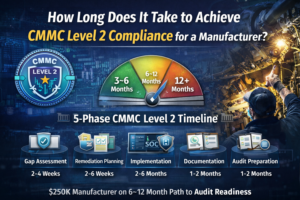
How Long Does It Take to Achieve CMMC Level 2 Compliance for a Manufacturer? For most aerospace and DoD supply chain manufacturers with 25–250 users,

What’s Included in Managed IT Services for CMMC Level 2 Compliance? Managed IT services for CMMC Level 2 compliance typically cost between $150 and $250

How Much Does CMMC Level 2 Compliance Cost for a 25–250 User Manufacturer? CMMC Level 2 compliance typically costs between $80,000 and $250,000+ in the

Introduction There is a widespread misconception across the Defense Industrial Base (DIB) that organizations have a three-year window to prepare for Cybersecurity Maturity Model Certification

Understanding the Context of Iranian Cyber Threats In the ever-evolving landscape of cybersecurity, one nation that consistently garners attention is Iran. Known for its sophisticated

Understanding the Zero-Click Exploit in iOS In the ever-evolving landscape of cybersecurity threats, the concept of a “zero-click exploit” presents a particularly insidious challenge. Unlike

Overview of the Cryptocurrency Market on 2/1 The cryptocurrency market experienced a tumultuous day on February 1st, marked by a significant plunge that sent shockwaves

Introduction to Notepad++ Vulnerability In today’s rapidly evolving digital landscape, software vulnerabilities have become a critical concern, demanding the attention of both users and developers

Introduction to AI in Business and Common Pitfalls Artificial Intelligence (AI) is no longer a futuristic concept confined to the realms of science fiction. It

Explore IT Careers in Seattle: Uncover Tech Job Potential Seattle remains one of the most competitive and opportunity-rich technology markets in the United States. From

Understanding Seattle’s Thriving Tech Scene Seattle, a vibrant metropolis nestled in the Pacific Northwest, is a beacon for tech enthusiasts worldwide. Known for its lush

Introduction to the Intersection of AI and Cybersecurity In a digital era marked by relentless innovation, Artificial Intelligence (AI) has emerged as a game-changer within

Understanding the Importance of AI Private Data Security In today’s digital era, artificial intelligence (AI) emerges as a transformative force, reshaping industries and enhancing efficiencies

Understanding the Importance of Cybersecurity in Today’s World In our increasingly digital age, the importance of cybersecurity has escalated beyond the realm of IT departments

Privacy regulations are evolving rapidly, and 2025 could be a pivotal year for businesses of all sizes. With new state, national, and international rules layering

Have you ever thought about how many potential customers leave your website because of accessibility issues? It’s not just a guess. A UK Click-Away Pound

Modern businesses depend on third-party apps for everything from customer service and analytics to cloud storage and security. But this convenience comes with risk, every

ChatGPT and other generative AI tools, such as DALL-E, offer significant benefits for businesses. However, without proper governance, these tools can quickly become a liability

Have you ever been concerned about your credit card or personal data getting stolen while shopping online? You’re not alone. Each holiday season, as millions

Microsoft 365 is a powerful platform that helps a business in many ways. It boosts collaboration and streamlines operations, among other benefits. However, many companies

Small businesses often struggle to leverage technology effectively. It can be a challenge just to survive, much less thrive. In many cases, they instinctively fall

The mass migration to cloud-based environments continues as organizations realize the inherent benefits. Cloud solutions are the technology darlings of today’s digital landscape. They offer

Data has become the lifeblood of every organization, regardless of industry or sector. Today, a business’s ability to collect, analyze, and act on data is

What would happen if your business lost all its data tomorrow? Would you be able to recover, or would it grind your operations to a

The landscape of remote work has transformed dramatically over the past several years. What began as a reactive shift to keep operations going during a

Choosing the right cloud storage solution can feel a bit like standing in front of an all-you-can-eat buffet with endless options- so many choices, each

For small businesses navigating an increasingly digital world, cyber threats aren’t just an abstract worry, they’re a daily reality. Whether it’s phishing scams, ransomware attacks,

Have you ever wondered how vulnerable your business is to cyberattacks? According to recent reports, nearly 43% of cyberattacks target small businesses, often exploiting weak

Microsoft 365 is a strong set of tools created to make working together and staying safe easier on many devices and systems. It has well-known

In this digital world, it’s hard to keep track of all the storage space on your devices. It’s easy for our devices to run out

You can make your computer experience more unique by changing the style of your desktop. It lets you organize your area well, which makes it

Malware is a huge threat in the digital world. It can cause a lot of damage and cost people a lot of money. As technology

It may seem like the file is gone for good when you delete it from your computer. However, the truth is more complicated than that.

Cybercriminals target Gmail a lot because it’s very popular. It also integrates with many other Google services. As AI-powered hacking attacks become more common, it

We use our devices every day, so they need to work well for our needs. A device that’s slow or broken is inconvenient and can

The Cyber Trust Mark is a new smart device label created by the US government to prove that a device is safe. Internet of Things
Mobile applications have become an integral part of our lives. We use them to browse the internet, network, communicate, and much more. But they open

AI is going to change how we work. It can make some tasks easier. But it can also cause problems. Let’s look at some ways

Our devices are a big part of our daily lives: work, fun, and staying in touch. Still, sometimes they make us less productive. In this

Ransomware has now become a big problem for many people and businesses. It can lock up your files and make you pay money to get

Data breaches can harm your business. They can cost you money and trust. Let’s look at how to stop them from happening. What is a

Malware is bad software that can hurt your computer or phone. It can also make your device run slow and steal your info. Here is

File storage and transferring hold a very dear place in most people’s lives. However, the safety of files is really tough to maintain. In this

These days, everything is digital. We deal with data every day: from personal photos to work files that hold a lot of value. What happens

In 2025, cyber threats are in almost every nook and corner. They might be with the intent to destroy computers, steal data, or take money.

Password managers keep our online accounts safe. They store all our passwords in one place. But are they hackable? What Are Password Managers? Password managers

In today’s fast-moving world, everyone wants to work wiser, not harder. The involvement of AI tools will definitely help you do just that. They can

Blockchain technology is changing the world. It is a system designed to keep records safe and secure. But how does it work? Let’s find out

Cyber hygiene is super important. It’s like brushing your teeth but for your online life. Good cyber habits help keep you safe from hackers on

Smart homes make life easier. But setting one up can be tricky. Here’s how to make a smooth smart home system. What is a Smart

Threat Exposure Management (TEM) is an important cybersecurity tool. It helps organizations find and fix weak spots in their digital systems. TEM outsmarts hackers before

Passwords unlock our digital lives. We use them for email, bank accounts, and more. Remembering all these passwords is hard. Password managers help us keep

The Internet of Things is growing day by day. More devices are connecting to the internet. And with that growth comes new security risks. Let’s

The pace of technological advancement is accelerating. This is not news to anyone wading through the ChatGPT craze. Artificial intelligence (AI) is at the forefront

Artificial Intelligence is no longer a technology reserved for companies with big budgets. Today, small businesses can access AI tools that help in several ways.

Customer service is at the heart of any successful business. Customer expectations continue to evolve. Companies must evolve strategies and tools used to meet those

Data breaches are an unfortunate reality for businesses of all sizes. When a breach occurs, the immediate response is critical. How a company manages the

Microsoft Teams continues to evolve. It is a powerful hub for collaboration and communication in the modern workplace. With the integration of AI-driven Copilot, Teams

Data is one of the most valuable assets a business can have. Managing this data throughout its lifecycle can be challenging. Data lifecycle management (DLM)

Email is a fundamental communication tool for businesses and individuals alike. But it’s also a prime target for cybercriminals. Cyberattacks are increasing in sophistication. This

Did your company’s software system once seem sleek and nimble? But now it resembles a tangled web of shortcuts, patches, and workarounds. Welcome to the

In the whirlwind of today’s business landscape, adaptability reigns supreme. Today’s workspaces transcend physical boundaries. Employees work and collaborate seamlessly from anywhere. Whether they’re sipping

Microsoft 365 is a powerful suite of tools. It helps to enhance productivity and collaboration. This is especially true for small to mid-sized businesses (SMBs).

In today’s world, everything’s connected. That includes the software your business relies on. Whether you’ve installed that software locally or use it in the cloud.

Your smartphone is a digital wallet, communication hub, and personal assistant. All rolled into one portable device. It’s packed with sensitive data, from financial information

A business network is the lifeblood of operations. It’s the digital artery that pumps data through your organization. It enables everything from email to critical

Buying a used laptop can be a great way to save money. But it comes with risks. You need to be careful and thorough in
The office landscape is undergoing a dramatic transformation. Gone are the days of sterile cubicles and monotonous routines. Today’s smart offices are hubs of innovation.

Windows 10 has served us well. But its time is running out. Microsoft plans to end support for Windows 10 on October 14, 2025. This

Traveling with technology has become a necessity. Whether for work, communication, or entertainment, we rely heavily on our devices. But traveling exposes these gadgets to

Imagine this: you walk into your office on a busy Monday morning, ready to tackle the week. But something’s wrong. Computers are unresponsive. Phones are

Running a small business is a whirlwind. You juggle a million tasks and wear countless hats. You also constantly fight the clock. What if you

Phishing has always been a threat. Now, with AI, it’s more dangerous than ever. Phishing 2.0 is here. It’s smarter, more convincing, and harder to

Is your smart home turning into a smart mess? Do your smart office devices speak different languages? You’re not alone. The current smart home and

The rise of remote work has redefined the modern workplace. Gone are the days of rigid office schedules and commutes. But with this flexibility comes

Gone are the days of paper-laden desks and rows of filing cabinets. The modern office is a hub of innovation. Technology plays a starring role

Artificial intelligence (AI) is rapidly transforming industries. It offers businesses innovative solutions and automation capabilities. But with this progress comes a growing concern: AI data

Smart homes seem like something straight out of a sci-fi movie. They have lights that respond to your voice commands and thermostats that auto-adjust. Not
Imagine this: you leave your house for vacation. You live in a shady neighborhood but feel confident your locks are secure, but you also don’t

Staying ahead of threats is a challenge for organizations of all sizes. Reported global security incidents grew between February and March of 2024. They increased

Microsoft Copilot has been heading up the business AI charge. It’s used in Word, Excel, Edge, Windows, and more. This genAI-powered app is also showing

Let’s face it, iPhones are amazing devices. But even the sleekest, most powerful iPhone can succumb to the dreaded slowdown. Apps take forever to load

Shiny new tech can be exciting! It promises increased efficiency, happier employees, and a competitive edge. It’s also necessary to stay competitive in today’s technology-driven

The annual Consumer Electronics Show (CES) was an exciting one this year. It left us with a mind-blowing glimpse into the future of technology. CES

Imagine a world where your lights turn on automatically as you walk in the door. Your coffee starts brewing before you even crawl out of

Data is the lifeblood of modern businesses. It fuels insights, drives decision-making, and ultimately shapes your company’s success. But in today’s information age, data can

Cyber threats are a perpetual reality for business owners. Hackers are constantly innovating. They devise new ways to exploit vulnerabilities in computer systems and networks.

What are some of the key differentiators that can propel small businesses forward? They include efficiency, productivity, and innovation. Microsoft has expanded the availability of

Calendars, task lists, and project planning are important business tools. Many people use Microsoft’s apps to power these processes. Including Planner, Microsoft To Do, and
The Internet of Things (IoT) is no longer a futuristic concept. It’s rapidly transforming industries and reshaping how businesses operate. IoT is a blanket term

It can be challenging to keep up with the ever-evolving cyber threat landscape. Companies need to process large amounts of data. As well as respond

Cloud computing has revolutionized the way businesses operate. It offers scalability, flexibility, and cost-efficiency. But cloud services also come with a downside: cloud waste. Cloud

We are living in an era dominated by digital connectivity. You can’t overstate the importance of cybersecurity. As technology advances, so do the threats that

QR codes are everywhere these days. You can find them on restaurant menus, flyers, and posters. They’re used both offline and online. QR codes are

Smart home devices are becoming more popular and convenient. But they also pose some serious security risks. Hackers can target these devices to access your

Cybersecurity is a constantly evolving field. There are new threats, technologies, and opportunities emerging every year. As we enter 2024, organizations need to be aware

Microsoft Edge continues to redefine user experiences. This is due to Microsoft’s commitment to innovation. The latest updates bring a host of features. These are

Relentless digital innovation has defined the last few years. The symbiotic relationship between AI and cybersecurity has become pivotal especially when it comes to safeguarding

Browser extensions have become as common as mobile apps. People tend to download many and use few. There are over 176,000 browser extensions available on

Staying ahead in business often means embracing cutting-edge technologies. New tools can unlock new avenues for growth especially for small businesses. SMBs are often looking

In the digital age, data is the lifeblood of businesses. It fuels operations, decision-making, and customer interactions. But there is a dark underbelly of this

The integration of smart home devices has become synonymous with modern living. They offer convenience, efficiency, and connectivity at our fingertips. But a recent study

Microsoft 365 has a powerful suite of cloud-based productivity tools. They can help you work smarter and faster. Microsoft has consistently been at the forefront

Artificial intelligence (AI) is a powerful tool. It can enhance the productivity, efficiency, and creativity of your staff. But AI also comes with some challenges

Gamers haven’t really been the focus of cybersecurity for a long time. You mostly hear about attacks on businesses. Or stolen personal data due to

Technology plays a pivotal role in driving efficiency, productivity, and competitiveness. For small businesses, workforce technology modernization is both an opportunity and a challenge. Embracing

Cybersecurity has become paramount for businesses across the globe. As technology advances, so do the threats. Recognizing this, the U.S. Securities and Exchange Commission (SEC)

Are you a small business owner or a freelancer who offers services online? If so, you might be wondering how to get paid by your

The global cost of a data breach last year was USD $4.45 million. This is an increase of 15% over three years. As we step

These days, our lives are intricately woven into the digital fabric. From emails to photos, documents to apps, our devices store tons of information. It’s

In our tech-driven world, electronic devices have become indispensable. But with constant upgrades, what happens to the old gadgets? They tend to pile up and

Technology is reshaping the world of work at an unprecedented pace. From artificial intelligence to web3, from the metaverse to the hybrid work model. We

Breached or stolen passwords are the bane of any organization’s cybersecurity. Passwords cause over 80% of data breaches. Hackers get in using stolen, weak, or

Cybersecurity has become a critical foundation upon which many aspects of business rely. Whether you’re a large enterprise or small business, network security is a

The use of AI-driven processes is exploding. Every time you turn around, software has gotten more intelligent. Harnessing the power of AI and machine learning

Imagine you’re working away on your PC and see a Windows update prompt. Instead of ignoring it, you take action. After all, you want to

In today’s world, sustainability isn’t just a buzzword; it’s a necessity. Businesses around the globe are increasingly embracing eco-friendly practices. This isn’t only for the

Smart homes have become a ubiquitous part of modern living. It doesn’t even seem unusual anymore to tell your refrigerator to add milk to the

Cybercriminals can launch very sophisticated attacks. But it’s often lax cybersecurity practices that enable most breaches. This is especially true when it comes to small

Software-as-a-Service (SaaS) has revolutionized the way businesses operate. It offers convenience, scalability, and efficiency. No more dragging software from one device to another. Everyone can

Endpoint management has changed a lot over the last two decades. There was a time when companies housed all endpoints in the same place. This

Two monitors are often better than one when it comes to getting things done efficiently. A dual-monitor setup can significantly enhance your productivity. This is

Let’s dive into a topic that might give you the chills—cybersecurity skeletons in the closet. You may not have old skeletons hidden away in the

As technology continues to advance, so does the need for heightened awareness. As well as proactive measures to safeguard sensitive information. Cybersecurity can seem like

Most people are familiar with their device’s Airplane Mode. You’ve probably used it when jetting off to exotic locations. But did you know that it’s

Apple’s iOS updates have always been eagerly anticipated. iPhone and iPad users around the world get excited to see what their devices can do next.

Running a small business can be challenging. But advancements in technology have opened a world of opportunities. Small business owners can use digital tools to

In today’s ever-evolving digital landscape, small businesses have more opportunities than ever. Many of these call for leveraging technology to their advantage. Embracing the right

LinkedIn has become an invaluable platform for professionals. People use it to connect, network, and explore business opportunities. But with its growing popularity have come

As technology continues to advance, so does the landscape of design tools. Microsoft has been a company at the forefront of business apps. Microsoft 365

In today’s digital landscape, cybersecurity threats continue to evolve. They pose significant risks to individuals and organizations alike. One such threat gaining prominence is zero-click

Remote work has become increasingly popular in recent times. It provides flexibility and convenience for employees. Additionally, telecommuting reduces office costs for employers. Many also

In today’s digital workplace, printing remains an essential function. This is true for just about all businesses. But keeping up with your print infrastructure can

Moving can be a chaotic and stressful time. Especially when it comes to handling your valuable technology. Whether you’re relocating your home or office, it’s

In today’s digital age, technology plays a significant role in our lives. But along with the rapid advancements and innovations, several myths have persisted. Is

Cybersecurity threats are becoming increasingly sophisticated and prevalent. In 2022, ransomware attacks jumped by 93%. The introduction of ChatGPT will only increase the potential damage

Advanced AI is a new buzzword in cloud computing. The launch of tools like ChatGPT and Bard have made big waves. Developers are now racing

Online shopping has become a common activity for many people. It’s convenient, easy, and allows us to buy items from the comfort of our homes.

As cyber threats continue to increase, businesses must take proactive steps. They need to protect their sensitive data and assets from cybercriminals. Threats to data

In recent years, electronic mail (email for short) has become an essential part of our daily lives. Many people use it for various purposes, including

What would you do if your business suffered a ransomware attack tomorrow? Do you have a contingency plan in case of a tornado, hurricane, or

In today’s world, technology is ubiquitous, and connectivity is a must. Securing your home network has become more critical than ever. A secure home network

Cloud account takeover has become a major problem for organizations. Think about how much work your company does that requires a username and password. Employees

Passwords are the most used method of authentication, but they are also one of the weakest. Passwords are often easy to guess or steal. Also,

Data visualization is a powerful tool for communicating complex data. It presents it in a simple, easily understandable format. But it is not enough to

It’s hard to turn around online these days without running into ChatGPT. Both Bing and Google are levering this advanced artificial intelligence language model. And

Companies both large and small share this one cybersecurity problem. They have computers that are still running older operating systems. Staff might use these devices

It’s a common theme. You begin seeing these amazing CGI images of your friends on Facebook or Instagram. You think, “How can I make one?”

Microsoft 365 is one of the most popular cloud platforms in the world, with about 345 million paid seats. Microsoft cloud tools numbers were up

The need to back up data has been around since floppy disks. Data loss happens due to viruses, hard drive crashes, and other mishaps. Most

Whether you sell shoes or run an accounting firm, you need some type of technology to operate. Today’s companies aren’t just in the business of

Technology vulnerabilities are an unfortunate side effect of innovation. When software companies push new updates, there are often weaknesses in the code. Hackers exploit these.
Imagine you’re going about your day when suddenly you receive a text from the CEO. The head of the company is asking for your help.

Misconfiguration of cloud solutions is often overlooked when companies plan cybersecurity strategies. Cloud apps are typically quick and easy to sign up for. The user

70TB of user data stolen from now-defunct social media site Parler.
Does it feel like you’re getting an email update from everyone you’ve ever done business with about how their company is handling COVID-19? A spike in corporate email

As companies collect and store more and more personal information, they face data privacy risks on many fronts. Increasingly, they are being held accountable for protecting

It can happen to anyone – you’ve taken steps to limit your exposure to a cyber incident. You’ve purchased and implemented top-of-the-line IT solutions. You’ve

Phishing is one of the most common, yet dangerous methods of cybercrime. It utilizes deceptive messages to trick victims into clicking untrustworthy links, downloading malicious

Maintaining compliance in today’s ever-changing environment is no easy task, particularly within the healthcare space. In the past, hackers opportunistically targeted providers due to poor

Data privacy regulations are quickly becoming par for the course in countries around the world, each one bringing new, nuanced responsibilities for companies to follow.

A quick glance at recent reports or news headlines paints a dismal picture of the data breach landscape in 2019. Both by the measure of

A data breach is disastrous for any company in any industry, but the healthcare sector is an especially high-stakes arena where data security is of

It’s no secret that the costs associated with data breaches are trending upward at alarming rates. Just this year, IBM’s annual Cost of a Data Breach

Few cyber threats are as prevalent and costly as phishing attacks. In 2018, Microsoft documented a 250% increase in phishing campaigns, which masquerade as legitimate products or

The remodel is finally complete! We have officially moved into our new building.

We will be moving into our very own building in July. The new building is also located in Kent so we will be calling Kent

Raj and Kamal co-chaired the 2019 South Sound Heart Ball on Friday April 26th. Under Raj and Kamal’s leadership, the campaign raised $400,000 – which

2018 was an amazing year for my personal growth and improvements, but I couldn’t have done it without having such a willing and able team
Meet Karson! When he isn’t working hard to resolve your I.T. issues, he is enjoying noodles at his favorite noodle place in Seattle Samurai Noodles.

Heart disease and stroke take the life of too many of our loved ones, yet most people don’t know that cardiovascular diseases are the number

We are celebrating our 5 year anniversary this year. It has been an amazing ride. In the 5 years, we have cultivated many relationships, clients

We welcome Roy to our growing team of technology enthusiasts. Roy was born and grew up in the Pacific Northwest. His interests are music and

On Saturday May 26th, inTech participated in the Annual Sikh Parade at the Showare Center in Kent. Heart disease is the leading cause of death

On Saturday May 19th, inTech had the privilege of volunteering for the Seattle Sluggers. The Sluggers are a Beep Baseball team from Seattle. Beep Baseball

We welcome Jake to our growing team of technology enthusiasts. Jake is originally from the state of New York. His interests are music, hiking and

Brayden was recognized as the Employee of the Year for 2017. We have a committee that recognizes and awards our team members monthly for Employee

Bitcoin, a type of cryptocurrency, has been the craze for the last couple months for its exponential growth and immense potential for profitability. For

In the previous blog post, we talked about our first speaking gig of 2018, on Cybersecurity. We talked about the importance of being very aware

As we get closer to 2020, we start entering the deep waters of immersive technology that can be very exciting but also worrisome. It is nice

As an organization, we want to give back to our community and it is our goal to have our team members involved in our community.

Everyone knows that there is a huge fan base for Apple’s iPhone. On September 12th, Apple is scheduled to make some interesting announcements and the

At one of our manufacturing customers, something strange was happening. Employee lunch was at 11:45am. That became 11:40am over several months. And it was only

It was Saturday Aug 26 and a beautiful Northwest summer day. We reached Rainier Beach High School and met with Kevin Daniel, coach for Seattle

We are remodeling our office to add more space for our new team. We have been growing pretty rapidly – adding 2-3 people per quarter

We are pleased to announce the expansion of inTech team to Vancouver, Canada. With our new office located at 8333 130th St, Surrey, BC. We

My days are hectic. My life is run by my calendar and therefore my iPhone. I am constantly checking emails, making calls and researching topics

When your phone dies at 36 percent battery remaining, you replace the battery. When the second battery does the same thing, and re-calibrating the battery

Come see us at our booth at the Kent Business Expo today at the ShoWare Center. Looking forward to meeting some great people.

Our team at inTech participated in the 2016 South Sound Heart and Stroke walk over the weekend. It was held at Cheney Stadium on Saturday,
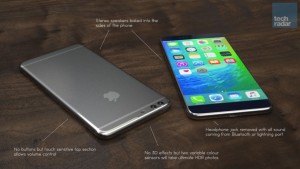
I get really excited at the beginning of September – every year. I am a huge Apple fan, iPhone fan, more specifically. Apple will announce
We are at the VMworld conference this year learning about all of the new technologies that are being introduced by the biggest names in the industry. We

We constantly come across a fair number of security related articles talking about security flaws, worms, viruses, Trojans and all manner of nasty sounding programs. With
MIT Rivals Tor What is Tor? Tor is free software for enabling anonymous communication over the internet. It stands for “The Onion Router,” based

The Current Landscape Right now, everything you do over any type of network is based on three types of cryptography, made popular in the
With the current direction the industry is heading, more and more IT environments are moving to cloud solutions. This means you need to use additional

The Basics of Security In any environment, the security system is only as strong as its weakest link. Why would you have a state

So you pay your employees to collect, input, process, correlate, audit and otherwise wrangle the data that drives your business. You’ve paid a small fortune

Business process automation (BPA) is a way to manage information, processes, and data with technology in order to reduce costs for a business. Because of

Secure your hardware Securing your hardware is an often overlooked and simple step you can take to secure your network. The best firewalls and anti-virus

We are always on the lookout for new talent, and as manager of our services team I interview a lot of candidates. Some are just

Remember that Sunday morning we set our clocks FORWARD by one hour! Daylight savings has to do with energy savings. Remember, this Sunday on March the
Office365 is a fantastic mail platform with many options. However, due to the large amount of options, certain features are often unexplored. Specifically, there seems

CryptoWall Viruses CryptoWall viruses such as CryptoLocker, AlphaCrypt and TeslaCrypt to name a few are ransomware trojans that encrypt any file that it has access

Looking for the bottleneck in your company? It most likely is technology. We all know, IT people can be difficult to work with. Hating the

Has technology become so important that we stopped paying attention to our surroundings, friends and loved ones? What happened to getting together with group of

It’s Monday morning at the office, and you just came back from a lovely trip to Hawaii. It was a long overdue break from the

You may have heard of Lexus creating a hoverboard, but that’s not this one! This hoverboard uses “Magnetic Field Architecture” (MFA) to hover around. Greg

Google has launched their new cute little autonomous vehicle (self-driving car)! Isn’t that neat? A few of the company’s prototype vehicles are now roaming the

Samsung’s latest hard drive – the 950 Pro SSD – is the fastest consumer SSD it’s ever made. The 950 Pro can reach speeds of

The cap-and-trade system, designed by China, will combat the country’s pollution levels by setting limits and charging companies for their greenhouse gas emissions. This will

Earlier this month, the El Faro cargo ship went missing around the Bahamas. Approaching the Bahamas, El Faro came in contact with 125-mph winds and

You can use Amazon’s Echo device to order a pizza or stream music on Spotify, so shouldn’t you be able to ask the digital assistant “Alexa” to

It’s a fact of life. Events out of your control can disrupt your business operations. While you can’t necessarily control the unexpected, you can take
Today we will discuss the importance of having your emails in the cloud and what options you have you to choose from.